Pol88 isn't just a simple player in the digital world. He conducts himself with an aura of mysteriousness, always two steps ahead of the competition. His tactics are shrouded in mystery, leaving his opponents clueless. Pol88 is a true artist of deception, crafting narratives that captivate. He leverages vulnerabilities with surgical precision, leaving a trail of confusion in his wake.
Pol88: An Exploration of Modern Digital Conflict
In the shadowy realm of cybersecurity/digital warfare/online conflict, a new threat has emerged, one that operates in the silent world of bits and bytes/code and algorithms/electronic signals. This is the domain of Pol88, a prolific/notorious/influential group allegedly/reportedly/supposedly engaged in high-level/sophisticated/advanced cyber attacks/operations/campaigns that target critical infrastructure/government agencies/financial institutions. Their motives are shrouded in mystery/secrecy/obscurity, but the scale/scope/impact of their operations is undeniable.
Experts/Analysts/Researchers are racing to uncover/decipher/understand Pol88's tactics, tools, and infrastructure/network/operations. The group's modus operandi often involves zero-day exploits/stealthy intrusions/targeted phishing campaigns, leaving behind a trail of disruption/damage/chaos.
- Governments/Security Agencies/International Organizations worldwide are heightening security measures/implementing countermeasures/launching investigations in an effort to combat this growing threat.
- The question remains: can we stay one step ahead of Pol88 and protect our increasingly connected/vulnerable/digital world?
Unmasking Pol88: Anatomy of a Cyber Threat
Pol88 has emerged as a malicious threat actor, deploying sophisticated cyberattacks across various industries. This widespread campaign showcases Pol88's advanced capabilities and its unwavering pursuit of sensitive information.
Analysts continue dissecting the inner workings of this threat actor, illuminating their tactics, techniques, and procedures (TTPs) to effectively counter their malicious endeavors.
Pol88's modus operandi often involves a multi-stage approach, commencing with reconnaissance. They then exploit vulnerabilities to gain access target systems, ultimately acquiring valuable data.
Measures are underway to mitigate the Pol88 threat. Security researchers work in tandem to develop effective countermeasures, train organizations about the latest threats, and enhance cybersecurity defenses.
Pol88 Implications
The emergence of Pol88 Pol88 has sent ripples through the cybersecurity community. Their sophisticated techniques have been observed targeting diverse organizations, raising concerns about their potential for large-scale disruption. Researchers are actively working to decipher Pol88's motives and capabilities, while organizations implement enhanced security measures to mitigate the risk of breach.
The sophistication of Pol88's operations highlights the need for continuous vigilance in the cybersecurity landscape. Dissemination of threat intelligence and best practices is vital to neutralizing this emerging threat.
Fighting Back Against Pol88: Strategies and Solutions
Pol88 is a dangerous threat that can wreak havoc on your devices. Battling it effectively requires a multi-faceted approach. First, it's crucial to deploy robust security measures on all your endpoints. This includes antivirus software and regularly reinforcing your software.
Furthermore, training users about Pol88 and its tactics is essential. Emphasize the importance of get more info being cautious with suspicious links and avoiding unverified sources. Fostering a culture of cybersecurity awareness can significantly reduce your risk.
Should you detect a Pol88 infection, it's critical to take immediate action. Isolate the affected device and seek expert support for eradication.
Remember, proactive defense is your best strategy against Pol88.
Pol88 Attacks: A Constantly Changing Threat
The threat landscape surrounding Pol88 attacks is rapidly transforming. Attackers are constantly leveraging new vulnerabilities and tactics to target systems. This ongoing evolution presents a significant challenge for security experts, who must remain vigilant and responsive in their efforts to address these threats.
Additionally, the ingenuity of Pol88 attacks is escalating. Attackers are now employing complex techniques, such as tool utilization, to perform attacks more rapidly. This trend underscores the urgent need for robust security strategies to stay ahead of these evolving threats.
- Security researchers are actively working to uncover new vulnerabilities and develop effective countermeasures against Pol88 attacks.
- Businesses must prioritize security awareness training and implement strong security policies and procedures to minimize their risk of becoming victims.
 Patrick Renna Then & Now!
Patrick Renna Then & Now!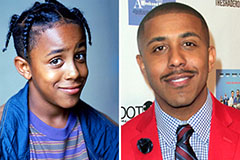 Marques Houston Then & Now!
Marques Houston Then & Now! Sydney Simpson Then & Now!
Sydney Simpson Then & Now! Hailie Jade Scott Mathers Then & Now!
Hailie Jade Scott Mathers Then & Now! Jeri Ryan Then & Now!
Jeri Ryan Then & Now!